Encryption, Privacy, Safe solution to communicate across Internet.
- Details
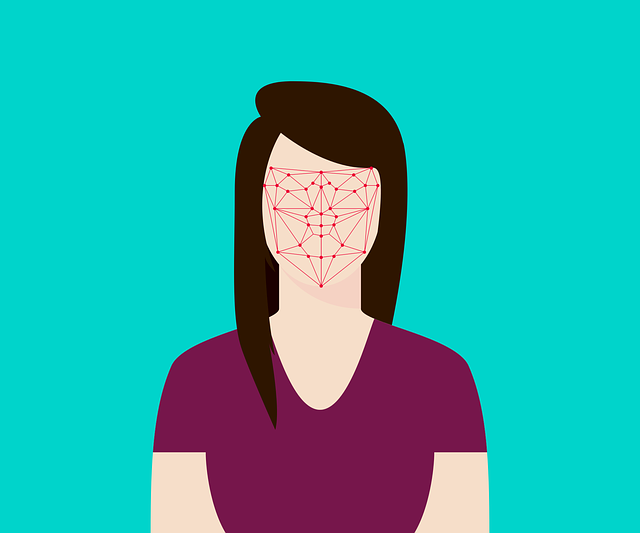
In a previous post, we discussed the massive number of video cameras in use worldwide and their use in facial recognition applications. With as many as 106,000,000 cameras being added yearly, an article posted on Interesting Engineering predicts there will be 45 billion cameras in use by 2022.
- Details
Operational technology, or OT, is the term widely applied to the networks that control industrial processes. These are the supervisory, control, and data acquisition (SCADA) systems and networks industrial and utility operations use to monitor, control, manage, and maintain the various processes they operate. For example, SCADA systems are essential in the efficient operation of the electric grid. OT systems are responsible for the oversight of the robots dedicated to assembly processes. Other OT systems control the flow of crude and refined petrochemicals in refineries.
- Details
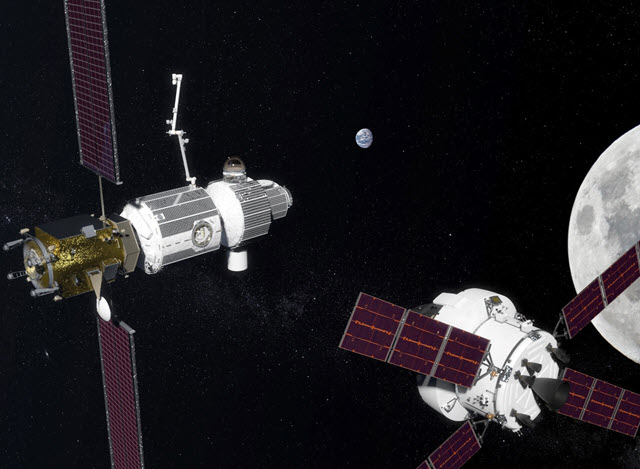
Our post today is a bit of a departure from the norm where we alert readers to the data and identity hazards of our digital world. In this post, we are looking at the sudden fascination space agencies around the globe are showing in our nearest celestial neighbor, the Moon.
- Details
Huawei is the second largest producer of smartphones in the world. In recent months, the US Government accused the company of including malware and spyware on their phones that enabled them to collect information from the phone and the area around it. In other words, it is a tool for espionage and cyber attacks.
- Details
This is the question a passenger flying on JetBlue had when she was asked to look at a camera for an identity check rather than use her photo ID. You can imagine how creepy and unnerving that may have felt. Especially since it was done without any prior notification at the airport.
- Details
The Electronic Version
Ever wonder where all the spam that floods email inboxes every day comes from? Turns out to be different than expected, at least as far as your author is concerned. According to the fine folks at Statista, China tops the list. During 2018, China produced nearly 12% of all worldwide spam. 11.69% for those wanting a more precise measurement.
- Details
There are ways of becoming less visible on the internet. Using the Tor browser is one, but that comes with its own risks, as our post discusses. VPN connections disguise your location, disrupting accurate tracking of your browsing habits. However, we leave tracks and histories in a growing number of places. If we want to protect our privacy and information, what other options are available?
About Skudo
We envision a world where all digital communications are safe and private. We are dedicated to creating innovative best-in-class hardware solutions that protect data exchange with the highest level of security and privacy.